HIPAA Compliance Services
Assessment, Advisory, Implementation
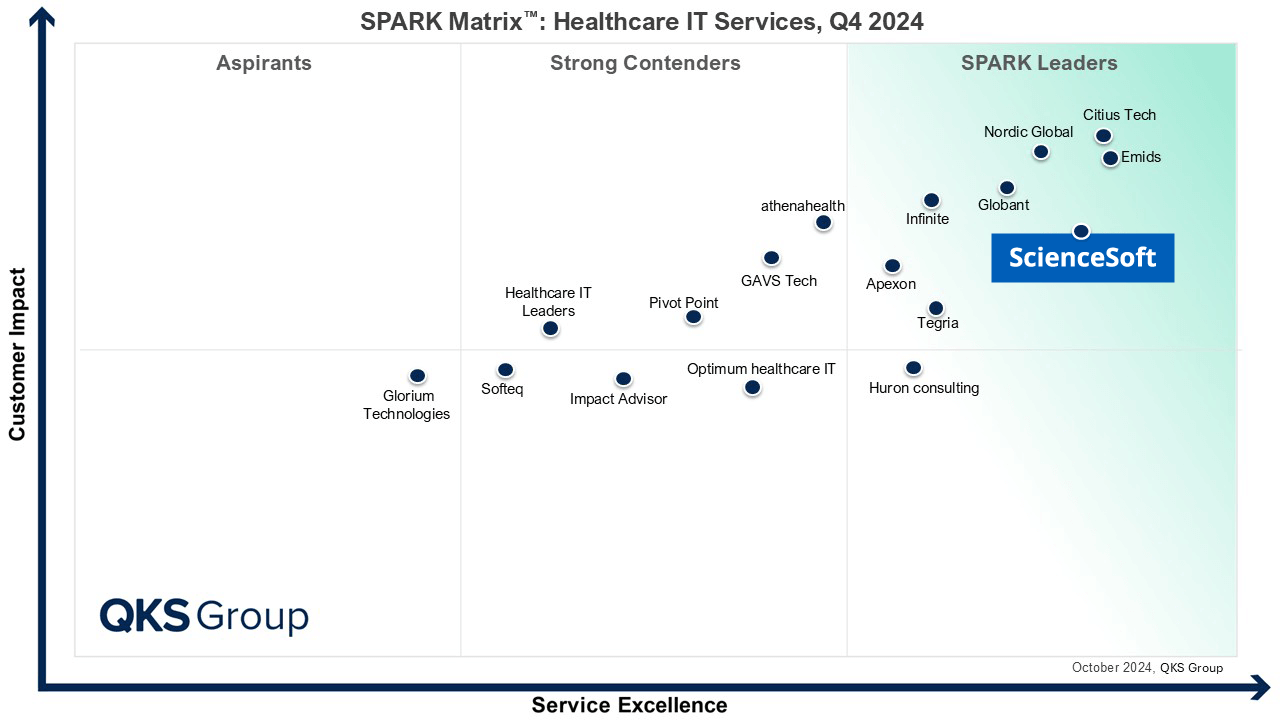
In healthcare IT since 2005 and in cybersecurity since 2003, ScienceSoft helps healthcare providers to achieve and maintain HIPAA compliance and software product companies to bring HIPAA-compliant healthcare solutions to the market.
HIPAA compliance services cover administrative and technical HIPAA requirements and can include establishing policies and measures to prevent or promptly mitigate PHI breaches, designing and building HIPAA-compliant software, migrating to a HIPAA-compliant infrastructure, and more.
Fighting Together for Better and Secure Healthcare
For organizations, compliance with HIPAA implies implementing policies, procedures, and technology that ensure the secure handling and proper use of protected health information, as well as timely data breach notification and remediation. For software vendors, it means ensuring that their product offers reliable health data protection. A HIPAA-compliant solution is software that incorporates such features as access controls, encryption in transit and at rest, secure communication, logging and monitoring, data backup, and disaster recovery mechanisms to secure PHI in line with HIPAA regulations. By taking charge of their security and compliance responsibility, we let the following businesses focus on their core work and make much-needed advances in the healthcare industry.
Healthcare organizations
Healthcare software product companies
Medical device manufacturers
Pharmaceutical companies
The Scope of HIPAA Compliance Services by ScienceSoft
PHI risks analysis and management
- Assessment of PHI breach risks.
- Developing a risk mitigation plan.
HIPAA policies and procedures review and improvement
- Analysis of existing security policies and procedures.
- Improvement recommendations.
- Design of missing policies.
Evaluating and promoting HIPAA compliance awareness
- Interviewing the staff and business associates on HIPAA provisions.
- Evaluating the HIPAA training process and materials.
- Recommendations on raising HIPAA awareness of the staff and business associates.
- Establishing an efficient training process, if needed.
Security assessment of applications and IT infrastructure
- Network architecture assessment.
- Vulnerability assessment.
- Penetration testing.
- App's architecture and source code review.
Implementing PHI security measures
- Implementing user access controls and user authentication mechanisms.
- Encryption of PHI in transit and at rest.
- PHI backup mechanisms.
- Establishing PHI breach detection and breach notification processes.
Securing IT networks
- Designing a secure network architecture.
- Installing and configuring firewalls, anti-malware, IDS/IPS.
- Implementing SIEM.
- Implementing identity and access management.
- Regular security assessments of the IT infrastructure involved in operations with PHI.
Designing and developing software in line with HIPAA
- Designing a comprehensive feature set for medical solutions.
- Translating HIPAA requirements into software requirements.
- Designing HIPAA-compliant development infrastructure.
- Designing a secure architecture.
- Advising on/implementing secure coding practices.
- Delivering convenient UX design for doctors, nurses, patients, etc.
- QA focusing on HIPAA requirements.
Medical software security and compliance improvement
- Detecting and fixing security flaws.
- Planning migration to a HIPAA-compliant cloud (e.g., AWS, Azure).
- Architecture re-design to improve PHI protection.
- Software evolution with the introduction of advanced security features.
Well-informed and trained employees play a critical role in maintaining HIPAA compliance. The best way to achieve this is to implement comprehensive compliance training that covers HIPAA provisions and best practices for data security. Ideally, it should include different modules for different user roles. Use real-world examples to make the training more vivid and social engineering testing as a mock drill for your staff. It is important to keep your training materials up to date, as HIPAA regulations evolve. New employees should undergo HIPAA compliance training as soon as they join the company. You should conduct regular training sessions to refresh your employees' knowledge and inform them about the latest requirements, cyber threats, and ways to handle them.
Deliverables You Get from HIPAA Compliance Services
Depending on the type and scope of the HIPAA compliance services, ScienceSoft provides a range of documents describing the service and its results. They may include:
Assessment deliverables
- Report on the existing security policies and procedures for PHI protection, gap analysis results.
- Network topology diagrams and network assessment against HIPAA requirements.
- Vulnerability assessment and penetration testing reports with description and prioritization of vulnerabilities endangering PHI and remediation measures.
- App's architecture and source code review reports with the list of identified deficiencies that could lead to PHI security breaches.
- Development infrastructure review with evaluation of its compliance with HIPAA requirements.
Advisory deliverables
- PHI security risk mitigation plan.
- Recommendations on implementing security policies and procedures required by HIPAA.
- HIPAA-compliant IT infrastructure design
- Resilient architecture design for HIPAA-compliant solutions.
- A roadmap to migration to a HIPAA-compliant infrastructure.
Implementation deliverables
- Description of infrastructure configurations enabling PHI protection.
- Diagrams of a HIPAA-compliant network.
- Designs of HIPAA-compliant software architecture.
- A feature list and prioritization plan for HIPAA-compliant applications.
- UX and UI design.
- Code documentation.
Benefits of HIPAA Compliance vs. Threats of Non-Compliance
Benefits HIPAA-compliant companies enjoy
- Improved data security. If properly implemented, proactive risk management and safeguards outlined by HIPAA requirements help avoid costly data breaches.
- Legal conformity that allows organizations to avoid litigations, fines or other penalties.
- Patient loyalty. HIPAA compliance showcases the company's dedication to protecting patients' privacy and security.
- Business partner trust. Organizations that prioritize data privacy are likely to opt for a HIPAA-compliant partner.
Threats noncompliant companies must consider
- Increased security risks, including data breaches and operational downtime.
- Legal actions and penalties for compliance breaches.
- Reputational damage. Potential clients are likely to dismiss services or products of a vendor that doesn't ensure their data privacy.
- Lost business opportunities. Noncompliant entities may be disregarded as potential partners due to concerns about the security and privacy of patient information.
- Increased regulatory scrutiny from the OCR that will require additional efforts and spending from the organization.
ScienceSoft as a HIPAA Compliance Company
- Since 2003 in cybersecurity.
- Since 2005 in healthcare IT.
- Established quality management system for medical devices and Software as a Medical Device backed up by ISO 13485 certification.
- ISO 27001 certification to ensure clients’ data security.
- Certified Ethical Hackers on board.
Learn the Cost of Your HIPAA Compliance Services
Answer a few simple questions to help us understand what services you need, and our healthcare IT consultants will quickly get back to you to calculate a quote.
Thank you for your request!
We will analyze your case and get back to you within a business day to share a ballpark estimate.
In the meantime, would you like to learn more about ScienceSoft?
- Since 2005 in healthcare IT services: check what we do.
- 4,200+ successful projects: explore our portfolio.
- 1,400+ incredible clients: read what they say.

Set High Expectations for HIPAA Consultants. ScienceSoft Will Comply
|
|
|
|
|
|
|
Don’t waste your time and money. To avoid unnecessary spending and efforts, we accurately define the HIPAA compliance service scope according to the size, complexity, and specifics of your business. |
|
|
|
Rest assured no HIPAA nuances will be missed out. Our team of HIPAA consultants, security engineers, and healthcare software developers can evaluate, implement, and enhance both administrative and technical safeguards as required by HIPAA. |
|
|
|
Contract a reliable vendor on beneficial terms. In case our cooperation continues, we can deliver subsequent services (repeated HIPAA compliance assessments, managed HIPAA compliance services, etc.) at a lower price in less time. |
|
|
|
|
Choose Your HIPAA Compliance Service
At ScienceSoft, we see our mission in driving your project success despite time and budget constraints, as well as changing requirements. We offer HIPAA compliance as a service or targeted help, practicing real project management to achieve your unique goals every time.
HIPAA compliance assessment
We assess how well a business or medical software meets HIPAA requirements and define measures to ensure HIPAA compliance.
HIPAA breaches remediation
We fix security gaps in your applications and IT infrastructure detected as a result of a PHI breach, OCR audit, or routine HIPAA compliance assessment.
HIPAA compliance program design and implementation
We help develop, establish, and maintain PHI security policies, procedures, and controls to achieve HIPAA compliance.
HIPAA-compliant software design and development
We employ our experience in healthcare IT and secure software development practices to architect and build top-level HIPAA-compliant medical solutions.
Challenges You Can Resolve with Our HIPAA Compliance Services
Complex and evolving HIPAA requirements
Bringing 19 years in healthcare and vast experience with HIPAA, we will outline, explain, and help fulfill the applicable requirements for your business or software. As we stay informed about regulatory updates, we are ready to assist you in adapting your compliance programs accordingly.
Lacking technical expertise
In IT since 1989, we know the nuances of apps and infrastructures of any complexity, including those that involve IoT, cloud, AR/VR, blockchain technology. This helps us not only reveal the compliance gaps, but also eliminate them, and not only plan compliance but develop the entire solution based on the HIPAA principles.
Prompt breach remediation and notification
Our expert team of HIPAA compliance consultants and cybersecurity engineers is ready to develop tailored breach response plans, investigate the breach and evaluate the risks, define and apply the necessary remediation measures, and guide you through the entire breach notification process.
Ongoing compliance monitoring
We provide continuous HIPAA IT support. This includes scheduling and performing regular compliance assessments to ensure that you remain compliant as your organization or software undergoes any changes or that you keep up with the latest HIPAA requirements.
Consistent risk management
Our IT expertise and knowledge of the healthcare industry allows us to accurately identify the threats to PHI and vulnerabilities in your IT assets and evaluate the risks. We can provide an actionable risk management plan with prioritized steps or implement the needed safeguards to keep sensitive health data out of danger.
Along with HIPAA Compliance Knowledge, We Rely on Proven Tools
With a solid portfolio of successful projects in healthcare IT and security testing, we have selected the best technology stack for HIPAA compliance testing and software development.
Common Questions About HIPAA Compliance, Answered
What does HIPAA compliance cover?
HIPAA compliance covers the set of measures on data handling and protection that businesses in healthcare must implement to ensure the privacy, security, and integrity of protected health information.
What are the most common HIPAA violations?
Some of the most frequent HIPAA violations include:
- Unauthorized PHI disclosure: e.g., posting patients' photos and medical conditions on social media without their consent, discussing sensitive health info with friends or colleagues.
- Failure to implement the technical safeguards required to secure PHI against data hacks: e.g., absent or weak encryption, misconfigured firewalls, antiviruses, and other security tools.
- Missing or inefficient employee training on compliance awareness. Employees' negligence or ignorance may lead to unintentional data exposure (e.g., sending sensitive data to the wrong recipient, gossiping about confidential health issues) or breaking security rules (downloading malicious files, clicking phishing links, etc.)
What are the different types of HIPAA compliance?
There are no different types of HIPAA compliance, but there are different categories of entities that need to be compliant:
- Covered entities, such as healthcare providers, health plans, and healthcare clearinghouses. They have broader obligations and are directly responsible for implementing all the measures required by HIPAA Rules.
- Business associates that handle PHI while providing services to the covered entities. They sign an agreement with covered entities that describes the permitted use and disclosure of PHI and the responsibilities of both parties for HIPAA compliance.
Is HIPAA compliance difficult and expensive?
HIPAA compliance can be challenging. The costs and efforts required to achieve compliance vary depending on the size and complexity of the organization. In any case, it means significant investments of money, time, and effort into policy design, security technology, employee training, and compliance assessments. However high the cost of compliance may be, the cost of non-compliance is always higher, as the consequences of a HIPAA breach may include heavy fines, reputational damage, and corrective actions imposed by the Office for Civil Rights or other enforcement agencies.
What is the most serious HIPAA violation?
The severity of HIPAA violations is evaluated based on the scope of the violation, the harm caused to the patients, the organization's efforts to prevent, report, and remediate HIPAA breaches, and previous non-compliance episodes. Here's an example of a very serious violation: a large-scale health data breach resulting from a phishing attack that was not reported and remediated in due time by an organization that had already been fined for unintentional patients' data exposure. This will be regarded as a Tier 4 violation (willful neglect, the incident was not rectified within 30 days), and the annual penalty may reach almost $2M.
What is not considered a HIPAA violation?
First, it is important to remember that not all health information is PHI. For example, HIPAA doesn't cover appointment registers or employee health records. It also applies to properly de-identified health data that couldn't be linked to a specific individual. Second, there are cases when sharing PHI is justified. For example, if a patient requires access to their health information. It is fine if PHI is shared between healthcare providers engaged in treating the patient — if only the minimum necessary information is disclosed for legitimate purposes. For investigation purposes, law enforcement officials can access PHI.
What are HIPAA compliance rules?
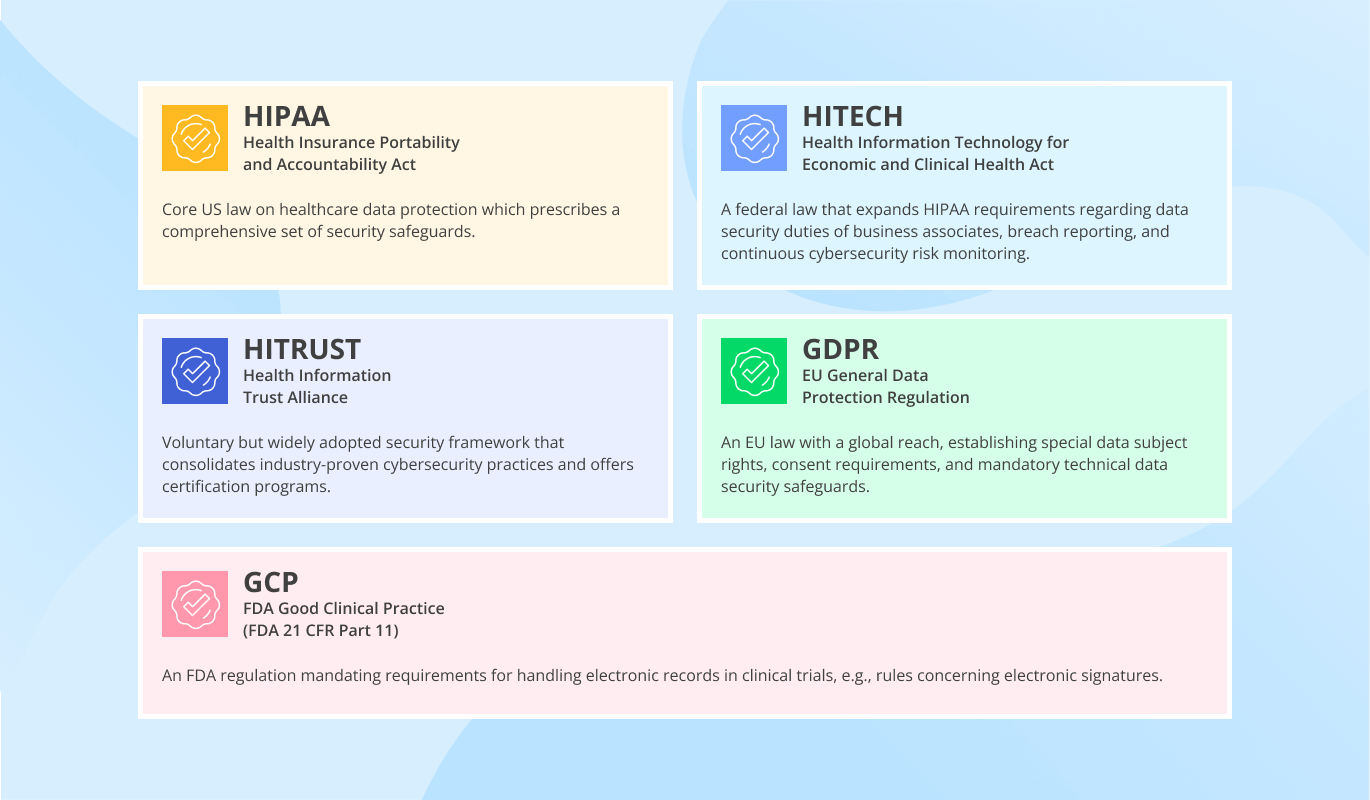
To achieve overall HIPAA compliance, organizations must comply with:
- The Privacy Rule that sets restrictions for PHI use and disclosure.
- The Security Rule that outlines administrative, physical, and technical safeguards to protect ePHI: e.g., employee security training, risk assessments, data encryption, incident response and recovery procedures.
- The Breach Notification Rule describing how a company should report HIPAA breaches to the regulatory authorities.
- The Enforcement Rule outlining procedures and penalties related to non-compliance.
- The Omnibus Rule that introduces significant modifications to HIPAA requirements: e.g., a more detailed risk assessment process, additional security controls, and heavier penalties for non-compliance.
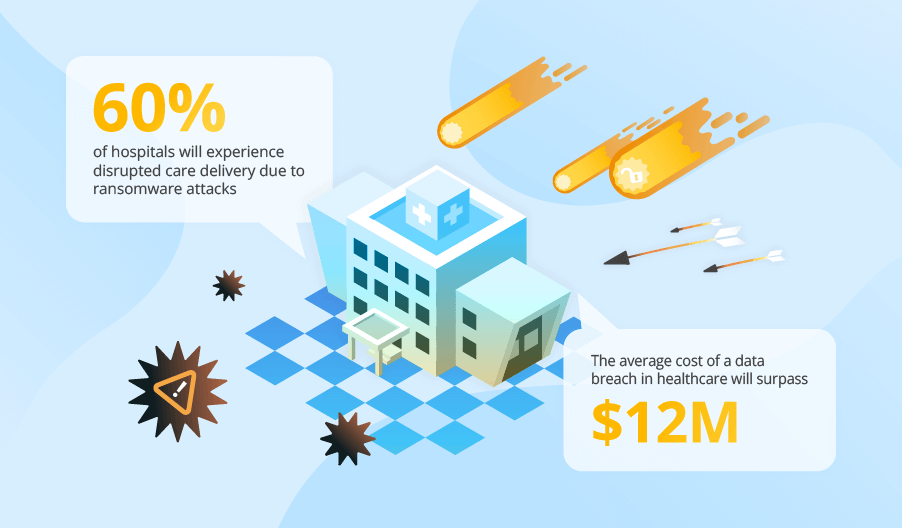
Why Safeguarding Health Data Is a Top Concern
|
$10M+ was the average cost of a healthcare data breach in the US in 2025 (IBM). |
56M+ individuals have been affected by healthcare data breaches in 2025 (HIPAA Journal). |