Cyber-Fortify Your Org with ServiceNow® Security Operations Platform
ServiceNow SecOps allows responding to urgent IT security issues quicker, search for and handle deep-lying IT security threats. Since 2010, ScienceSoft has been implementing ServiceNow SecOps solutions to help companies minimize risks of cyberattacks and raise their IT security threat awareness.
Want to visualize your ServiceNow Security Operations solution before embarking on the implementation journey? Then you can request a live SecOps demo from our ServiceNow consultants right here!
ServiceNow SecOps Features
ServiceNow Security Operations does not replace security tools like SIEM, IAM, DLP or the like – it aims to bring clarity, insight, collaboration and business-driven prioritization into the daily routine of your security specialists.
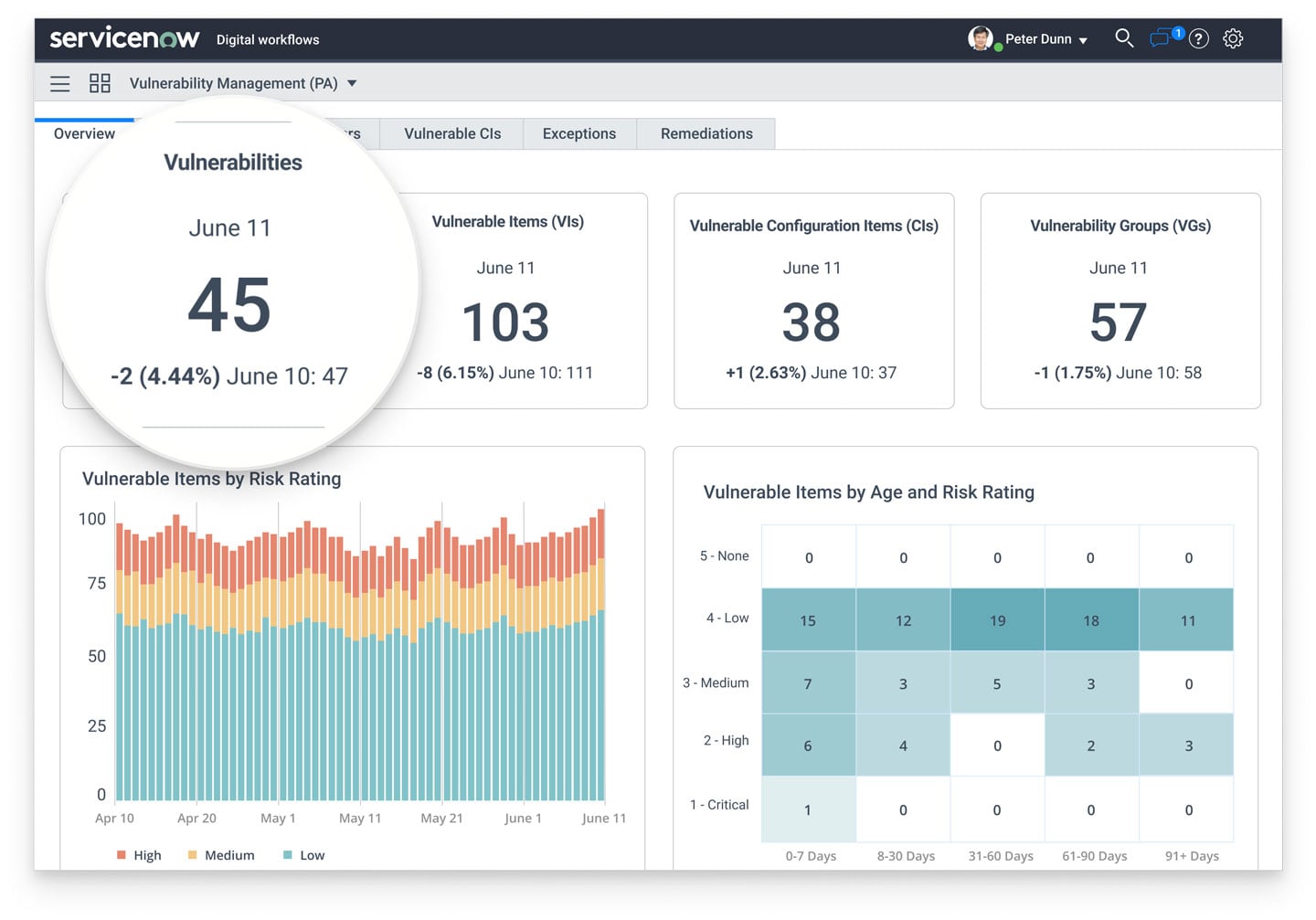
Vulnerability Response
Comparing information from vulnerability scanning tools with the information in your Configuration Management Database (CMDB), Vulnerability Response puts the scan data into the context of your business and IT services. Then, it filters the pool of detected vulnerabilities and prioritizes them according to factors like business impact and technical severity. Doing all that, Vulnerability Response enables your security agents to quickly remediate business-critical vulnerabilities and also collaborate with the IT team in requesting and enacting needed changes in the IT infrastructure.
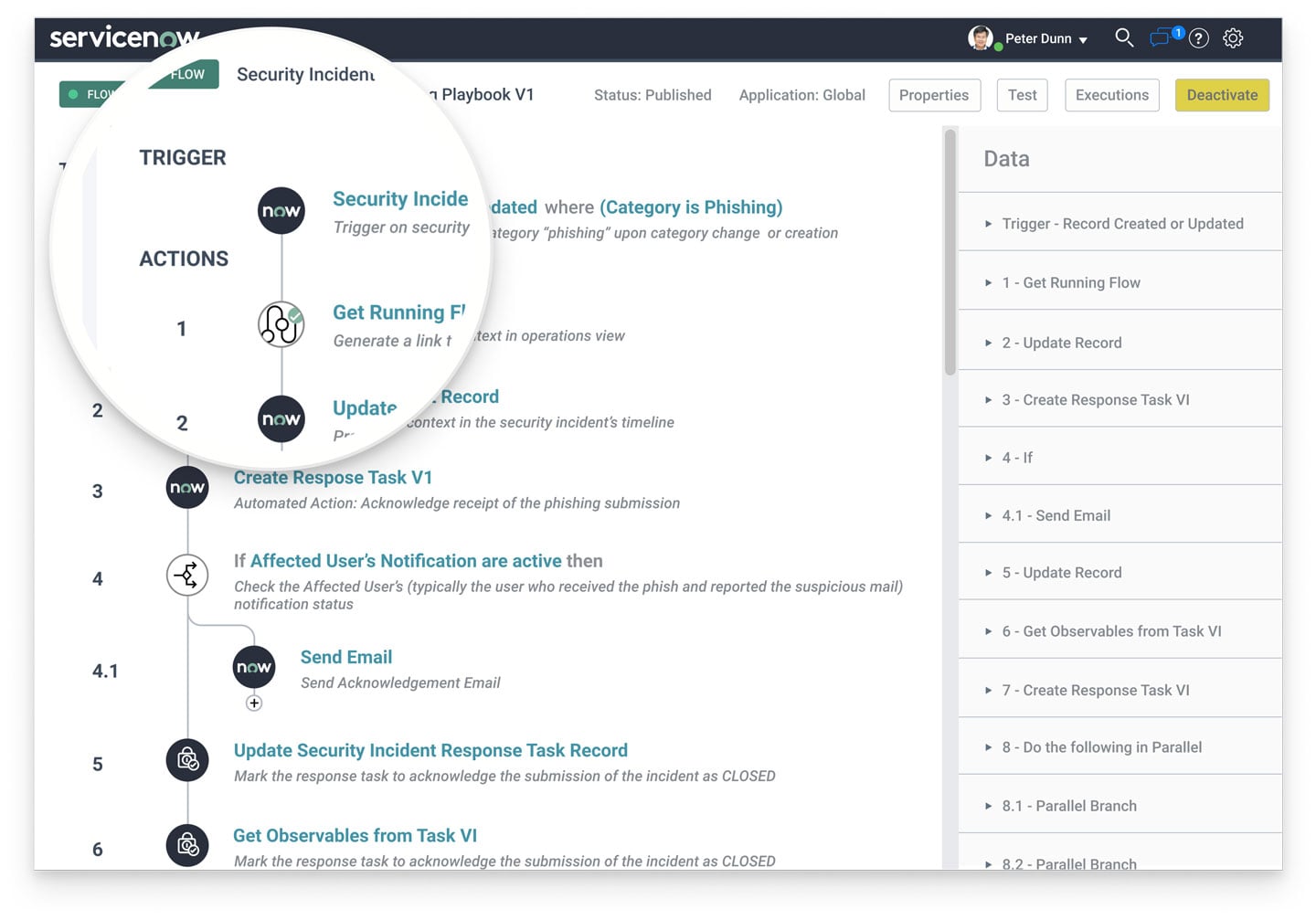
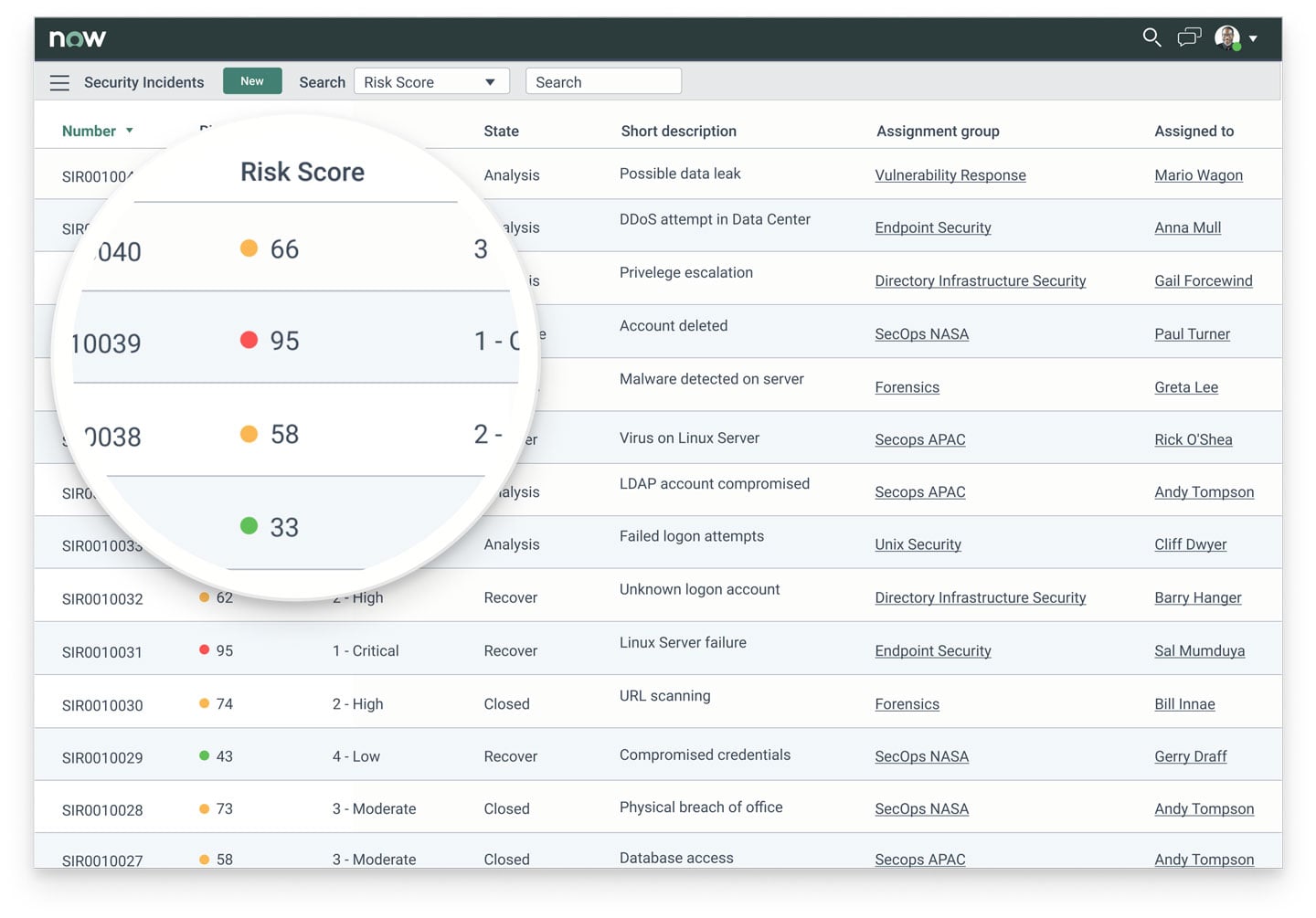
Security Incident Response
ServiceNow imports suspicious activities in your infrastructure from your security tools like QRadar, Splunk, Rapid7, etc. Security Incident Response automatically converts these activities into security incidents, uses your CMDB to prioritize them and later assigns them to security responders. Using an intuitive workspace, security teams bring incidents from analysis and investigation to containment and remediation. To increase your security team’s productivity, ServiceNow breaks down each security incident into separate tasks and supports the usual task completion paraphernalia like automation workflows, notifications, SLAs, escalation rules, etc.
Threat Intelligence
Through integrations with security monitoring tools and specialized threat data websites, Threat Intelligence notes indicators of compromise on your network (or in an operating system) and checks threat feeds to find intel on new vulnerabilities, software errors, hack groups and so on to enrich your security incident records with more relevant information. This gives security specialists the insight for detecting and analyzing deep-lying threats better. To help recognize if any security incidents, indicators of compromise or observables relate to a targeted attack campaign, Threat Intelligence allows consolidating these entities to be handled as joint security cases.
Trusted Security Circles
To detect and eliminate threats faster, ServiceNow SecOps allows you to anonymously share questionable observables (IP addresses, hashes, URLs) and other threat intelligence data with a predefined network of companies. The network can involve your industry peers, supply chain partners or even the global community of ServiceNow customers. If the threat data you shared was observed often enough among your network members, ServiceNow can automatically start the process of remediating this threat as a security incident.
Configuration Compliance
Looking at data imported from configuration scanning applications, Configuration Compliance identifies vulnerable assets that are not configured according to your security or corporate policies. Then, it prioritizes them by checking their potential business impact in your Configuration Management Database (CMDB). Configuration Compliance helps to diagnose and remediate more vulnerable assets, thus strengthening your security posture further.
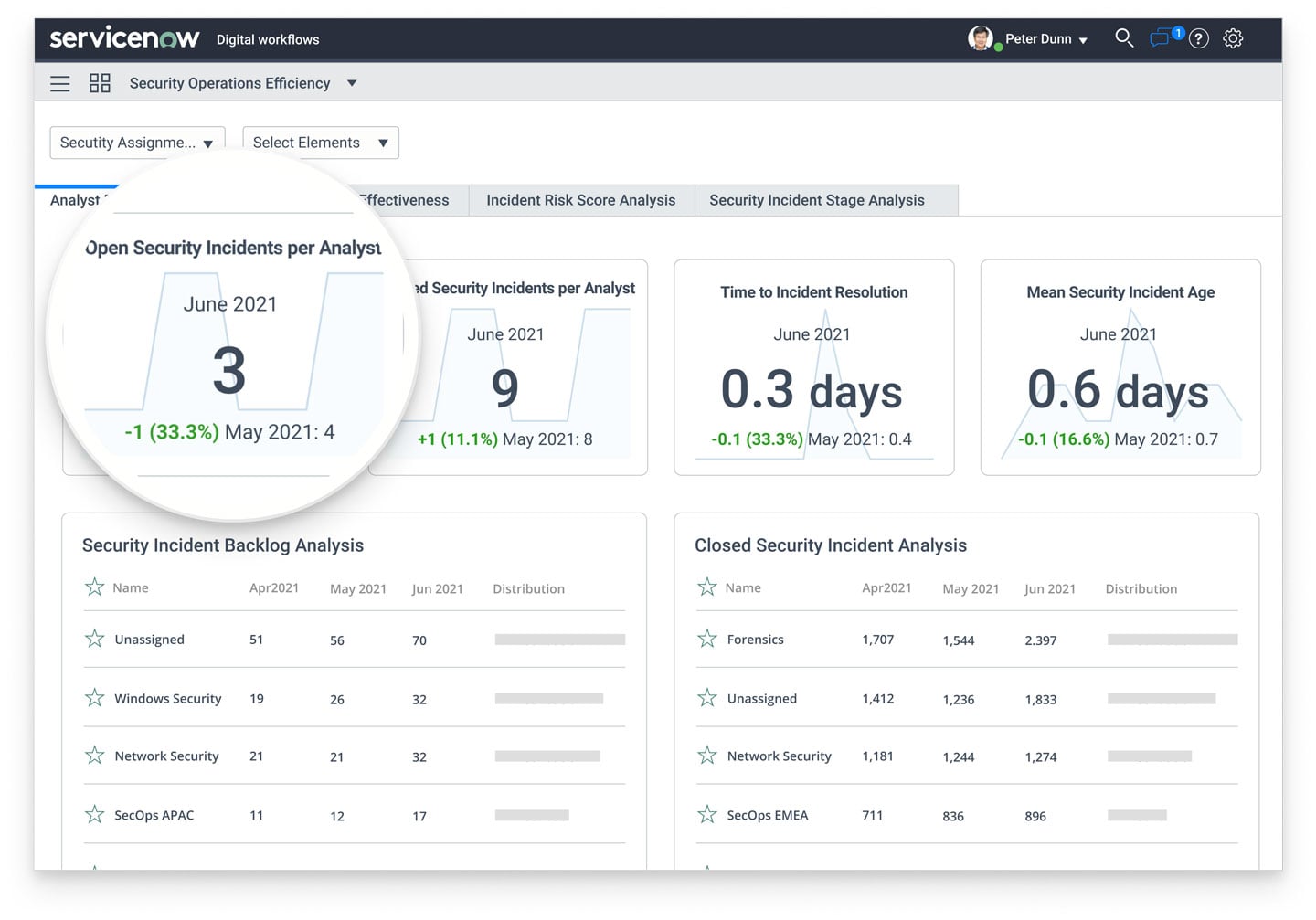
Performance Analytics for SecOps
With pre-defined and custom SecOps key performance indicators, reports and dashboards, Performance Analytics empowers you to gain valuable insights into your security operations. It leverages the data in your ServiceNow SecOps and helps you reveal trends and bottlenecks in your procedures as well as discover automation opportunities for some of the manual tasks performed by your security responders.
Integrations with Other Products
Being dependent on other security and IT tools, ServiceNow Security Operations needs to be integrated with enterprise systems and applications, such as:
- CMDB, Event and Change Management modules of ITSM systems (either ServiceNow-based or external).
- SIEM, IAM, DDoS protection, DLP and IDS/IPS applications.
- Governance, Risk and Compliance solutions (either ServiceNow-based or external).
- Network and vulnerability scanning applications.
- IT infrastructure management solutions.
ServiceNow SecOps Packages and Pricing
* Limited number of queries allowed
** Enriched with Orchestration workflows to automate repetitive infrastructure-related security tasks
ServiceNow SecOps Implementation Insights
Benefits:
Improve your security posture by:
- Identifying and handling more critical threats first
- Cutting response times and increasing response efficiency
- Reducing the severity of attacks’ impact
Foster your security team’s productivity with:
- Step-by-step playbooks for quicker incident remediation
- Knowledge base articles on previously handled incidents
- Task automation (e.g., for firewall block requests)
Implementation strategies:
CustomizeServiceNow to support your SecOps processes without changing them. |
Modifyyour SecOps processes to reflect ServiceNow’s best practices, ergo avoiding heavy customizations. |
Evolveyour SecOps processes to eliminate their shortcomings and customize ServiceNow accordingly. |
Stages:
1
Requirements gathering
Starting with investigating your security operations-related needs and resulting in a thorough requirements specification
2
Configuration and customization
Supplemented with migrating data and doing integrations and QA
3
Production rollout
Training your users, putting the solution into production and delivering 2-3 months' after-launch support
Optional stage: a pilot project (implementing an exploratory small-scope solution before the major implementation project to better picture the outcomes that your major implementation project will bring).
Possible risk:
|
|
Meager business value of the SecOps solution due to faulty security tools or processesSolution: reviewing the performance of your security tools (including SIEM and network scanners) as well as the efficiency of your security processes to perform needed tool or process adjustments before implementing ServiceNow SecOps. |
As a Registered ServiceNow partner, ScienceSoft can deliver reliable ServiceNow implementation services and enrich them with our extensive 20+ years of cybersecurity expertise to make sure that your ServiceNow SecOps solution will deliver the promised business value and achieve a substantial ROI.
Other Related Services We Provide
Testing
Custom app development
Integration