Session Mapping to Facilitate User Identification with IBM QRadar SIEM
Related topics:
Last updated:
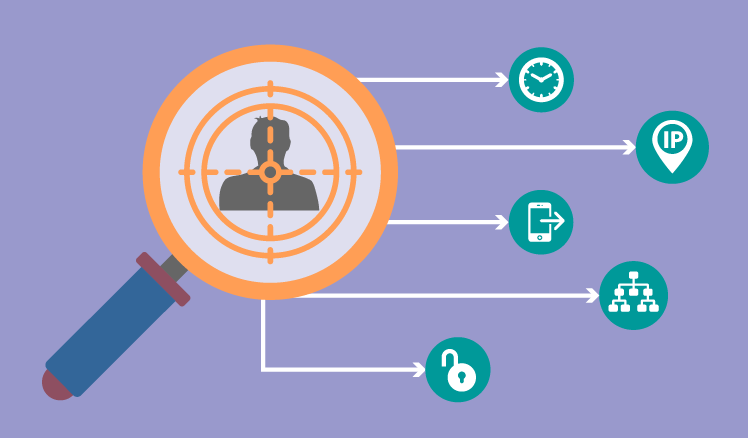
Placing a SIEM solution at the core of their information security, companies hope not only to get comprehensive information on all the offenses that threaten their IT environment, but also to detect attackers and their actions. However, even such an advanced SIEM system as IBM QRadar SIEM (QRadar), a leader in 2018 Gartner’s Magic Quadrant for SIEM, which processes and correlates huge amounts of security events, has one weakness. While informing security administrators on offense types, their severity, source and destination IPs, QRadar often leaves uncovered both user names behind those IPs and actions that have triggered the offense in the first place.
With only IPs known, identifying a real intruder becomes a tough task with a high risk of false results, especially if a QRadar administrator deals with dynamic IPs that may be used by different users.
Discovering real users with QRadar Session Manager
Trying to solve this challenge, ScienceSoft’s SIEM consultants came up with an alternative way to get closer to user identification in QRadar via the dedicated tool called QRadar Session Manager that analyzes user sessions, i.e. a period of time when a user is logged under a single IP. Consisting of a server and a UI, the tool discloses user names via an IP address (or vice versa), as well as shows user activities performed during a particular session.
Such a tool can be implemented as an integral part of QRadar to investigate security events by analyzing session information, even if no user name is available in an initial log message. To make sure a session is unique, this tool uses predefined conditions of session termination, such as:
- A user’s logoff.
- Authentication of a new user on the host with a session opened by another user.
- A session timeout.
- High-availability cluster switch.
- The tool’s server termination/restart.
Investigating a user session
By finding out the session start and end time and the IP address, a QRadar administrator will be able to discover a user(s) behind these IPs as well as to see all the log sources that report the user’s presence during the session.
To go even deeper, security administrators can conduct a detailed investigation of a session by disclosing user activities across all the listed log sources and getting the following information:
- Event time.
- Log source.
- Event category.
- Event name.
- User name.
- Source IP.
- Destination IP.
- Destination port.
- Any common normalization field available.
- Any custom property available.
According to the investigation scope, the list of activity attributes can be either expanded to include all the variables, or narrowed down to reflect selected characteristics only.
Analyzing sessions to disclose security threats
Information provided by the session mapping tool together with QRadar data enable security administrators to carry out quicker and more targeted investigations of offenses originated from both internal and external users.
Enforcing an internal security policy. Even regular corporate security training cannot guarantee users’ adherence to their security policy. Negligent user behavior and security policy violations often lead to compromising corporate assets and data. Trying to pinpoint a policy violation and detect a negligent user via standard SIEM features, security administrators and analysts need to sift through huge amounts of data while correlating scattered violations is impossible altogether.
At the same time, using the session mapping approach, a security administrator can discover a security policy violation by disclosing negligent users and their vulnerable actions (even if they were performed in different periods of time), then to apply adequate measures.
Counteracting malicious insiders. The tool can also help to detect users performing harmful actions intentionally, in order to expose a corporate infrastructure to external attacks or severe breaches. Analyzing users’ activities via session mapping, security administrators can detect malicious insiders and get detailed information on their actions, thus prevent major leaks of sensitive data.
Detecting outsider threats. The same approach can help to deal with outside attacks. Once an attacker starts a session in the corporate network, all his/her actions get registered and become available for analysis. Detecting an outsider's malicious activities can help to identify both one-off and persistent attacks before they engender devastating data and money losses. Moreover, session mapping can become an important technique of an APT detection, thus let security administrators detect intruders quicker and block their presence within a network.
Getting an all-round view of users with SIEM
The presented approach to managing security events is one of the possible ways to enhance the value of a SIEM system. Session mapping doesn’t replace the entire array of techniques provided within a SIEM, however, it helps security administrators with the following:
Getting specific information not available in the SIEM solution. Session mapping can bridge the gap between an offense and the user actions that triggered it, thus providing QRadar administrators with necessary information to analyze a particular offense in-depth and reveal both negligent and malicious users.
Reducing the time spent on security investigation. Using the session mapping approach, security administrators can save valuable time by identifying user names and activities without spending additional efforts on event analysis and correlation in QRadar.
To learn more about the session mapping tool and its integration with IBM QRadar SIEM, please feel free to contact us. Our SIEM team is always ready to offer you a free consultation or to make a live presentation of the solution.

