Java microservices for project managers
Related topics:
Last updated:
Microservices are an architectural solution for designing complex software by breaking it into small independently deployable modular services. It is often contrasted with the traditional monolithic architecture where software is built as a single unit. Most often, microservices communicate via REST.
Let’s consider how introducing microservices can help a Java project, what efforts their introduction requires, what risks it brings, and in which cases it will not be a good fit.
Short summary:
- The good about microservices
- The bad about microservices
- Microservices use cases
- Microservices and information security
- Skills required for microservices project team
- Test strategy for microservices

Advantages
Java microservices architecture brings the following benefits to a project:
- Opportunity to deploy, rebuild, redeploy and manage software modules independently. It allows you to involve different project teams for Java application development and write code for microservices in different programming languages.
- Opportunity to apply the latest technologies to deploy a new service. Developers are free to choose whatever technologies make sense and are no longer obliged to use possibly obsolete technologies applied at the project start.
- Fast software deployment. Developers can deploy their modules independently without having to wait until the other components are ready.
- Continuous software delivery. Software modules can be continuously delivered in parts.
- Ease of understanding and modifying software. Small pieces are easier for new team members to learn, so they get into the project quicker.
- Improved fault isolation. Failure of a single module does not affect the rest of the application.
Drawbacks
As everything goes for its price, let’s consider some potential pain areas associated with implementing Java microservices:
- Difficulty in coordinating multiple services. Developers have to put additional effort into microservices integration.
- Increased effort for operations, deployment and monitoring. Each microservice is a separate deployment unit that has to be released, tested and monitored. Besides, each service needs a separate database.
- Cumbersome change process of mutually reliant services. If you need to make a change that affects several interdependent services, you will have to modify all the services involved. This procedure also requires cooperation between different development teams.
- Complicated and tedious testing. You will need to test each service together with all the services it depends upon.
- Duplication of memory use. Several classes and libraries are often duplicated in microservice bundles, which increases memory footprint.
When microservices are not suitable
Considering the benefits and drawbacks the Java microservice architecture brings to a project, it makes sense to apply it for complex evolving applications where a monolithic architecture becomes too difficult to manage. As for short and simple projects, there’s no need to invest deployment and testing efforts into microservices.
Is a mixed approach possible?
Can you kill two birds with one stone and combine the monolithic approach with the microservice architecture? Unfortunately, you cannot. However, you can order to refactor your monolithic application to microservices if there’s such a necessity. This process is rather complicated, but it will make sense, if you are sure that your application is going to grow soon.
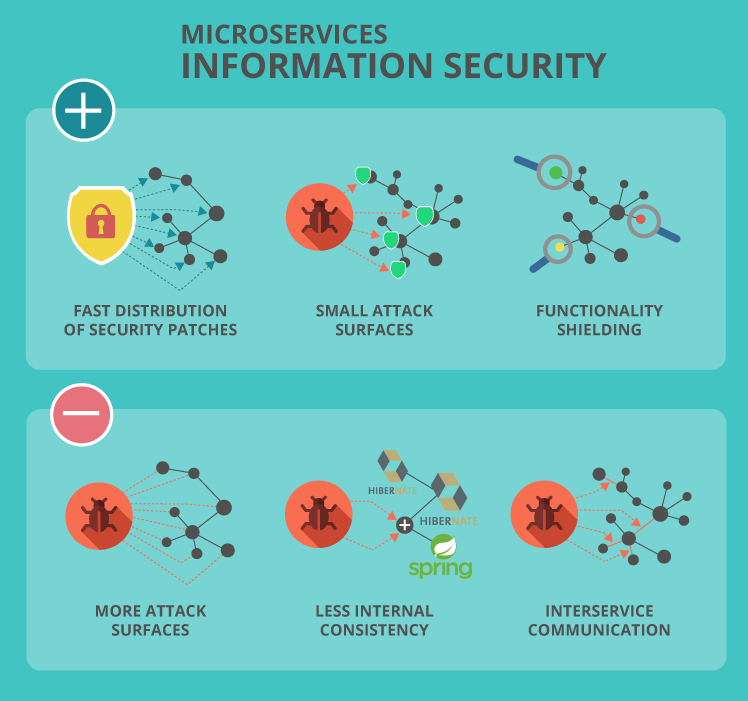
Information security
Java microservices can both improve and reduce an organization’s security posture. Let’s see how microservices help ensure application security.
- Fast distribution of security patches. Due to their distributed nature, microservices make patch deployment easier and quicker. Security updates can happen once or twice a week or even multiple times a day with microservices, while with a monolithic architecture such updates occur once or twice a year.
- Small attack surfaces. Each microservice provides a restricted set of functionality, which results in smaller attack surface than in the case of monolithic applications.
- Functionality shielding. Microservices spread out the software functionality, which simplifies the task of security staff. They can focus on reviewing a particular service’s functionality instead of tracking the app’s functionality on the whole, which accelerates security reviews and makes the results more accurate.
Yet, microservices may introduce some soft spots to your Java project security.
- More attack surfaces. The more modular services software has, the more potential vulnerabilities they have.
- Less internal consistency. Developers can switch among various frameworks introducing new microservices, which leads to less software consistency compared to monolithic applications. Whenever something changes, there is a chance that a new security vulnerability may emerge.
- Interservice communication. Microservices communicate over the network, which creates more inroads for attacks on transit data.
How to solve security problems
With the right strategy, the security risks associated with the microservice architecture can be mitigated.
Start with establishing common repeatable coding standards to reduce code disparities that can lead to exploitable vulnerabilities or escalated privileges. Then, take care to provide permissions to software modules only to the processes or individuals that should have it. For example, a microservice that merely checks the inventory availability should be granted read rather than read/write permissions to access a database if there is no necessity to modify the existing information.
Map out communication methods among microservices. This will help identify potential problem areas as well as the application’s irregular behavior. And, finally, keep each microservice fully documented, including the function it serves, what damage can be done to (or by) each particular microservice if it is compromised, and what it can be adjusted to or safeguarded against.
Bridging skill gap
Let’s consider what technical knowledge a Java developer needs to work with microservices.
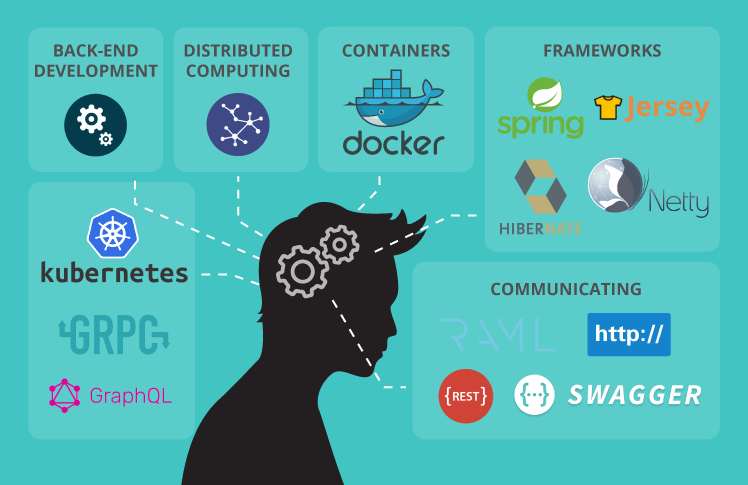
First of all, one should be familiar with distributed computing. Microservices are a distributed system that is more complex than a traditional monolithic architecture. So, each microservice should solve only one problem not to overcomplicate the system. Besides, the project team should be prepared to refactor software elements as needed.
Knowledge of containers, perhaps, the most popular ones such as Docker, may be useful. They allow software to run reliably every time and help pieces of code be plugged into the operating system quickly.
As there are lots of complexities in getting microservices work together, experience in back-end development will be useful for developers as well.
Since Java microservices are typically communicating REST over HTTP, understanding REST/HTTP/RAML/Swagger is also required. Other useful technologies include Kubernetes for service orchestration, gRPC for high-speed internal communication, GraphQL for data orchestration, and so on. Among the most used frameworks to work with microservices in Java are Spring, Hibernate, Jersey, and Netty. These are open source frameworks praised for their reliability, maintainability and high performance.
Testing microservices
Considering the modular nature of the microservice architecture, testing gets rather tricky with multiple layers required.
- Unit Testing. Small pieces of software such as a method in a microservice are tested.
- Component Testing. At this stage, a microservice is tested in isolation.
- Integration Testing. Interservice communications and interactions are tested to detect interface defects.
- Contract Testing. Contract tests verify interactions at the boundary of an external service to check that the system works as specified in the contract.
- End-to-End Testing. At this stage, testing engineers check how the entire system works as a whole and whether it satisfies the project requirements. They also check if there are any high-level disagreements among the microservices.
Afterword
Considering benefits Java microservices bring to the software development process, no wonder they are becoming increasingly popular. But you should remember that everything goes for its price and carefully weigh the pros and cons of this architecture against your needs.


